Penetration test report cisco router
Description




Hi guys Katy Age: 23. Partake in a unique experience with a beautiful, sensual womanI have the ability to make you feel at ease right away.Hi guys im kiana????


Nancy Age: 35. If your looking for a fun,sensual,seductive and naughty playmate I am the one for youI am Sandra, im attractive, independent, intelligent

cisco products | Penetration Testing Lab


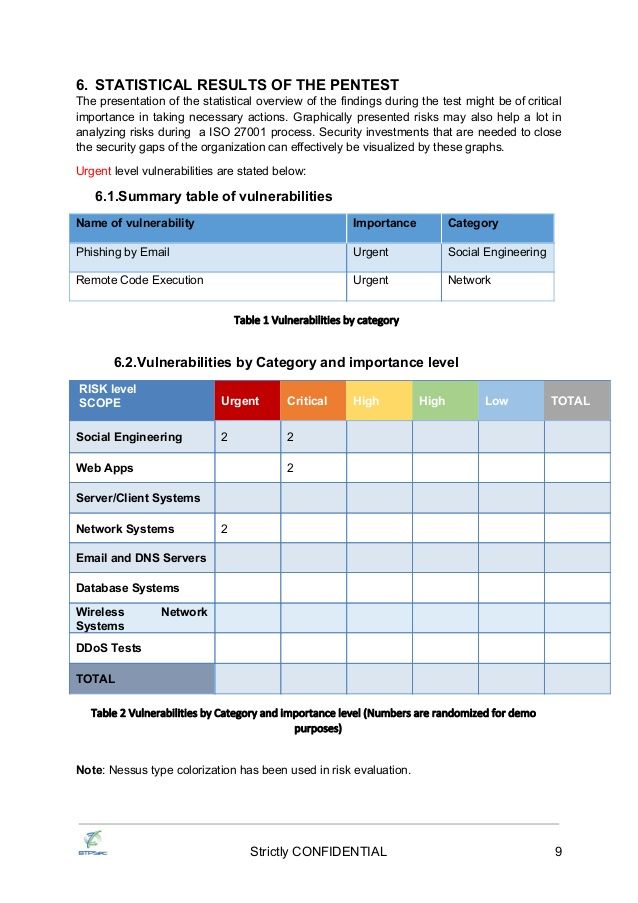

13 May Penetration-Testing. Hello experts,. Im a CCIE, but Im totally new to the penetration-testing world, i dont know anything about pen-testing. some one (an external company) has asked me to do a penetration-testing on their netwrok through internet. Can anyone advise me what to do? is it just easy to. Writing a penetration testing report is an art that needs to be learned to make sure that the report has .. Appendix A shows a Sample report of a penetration testing.
4. References. Whitaker, A., & Newman, D. (). Penetration testing and network defense. USA: Cisco Press. Smith, B., LeBlanc, D., & Lam, K. () .

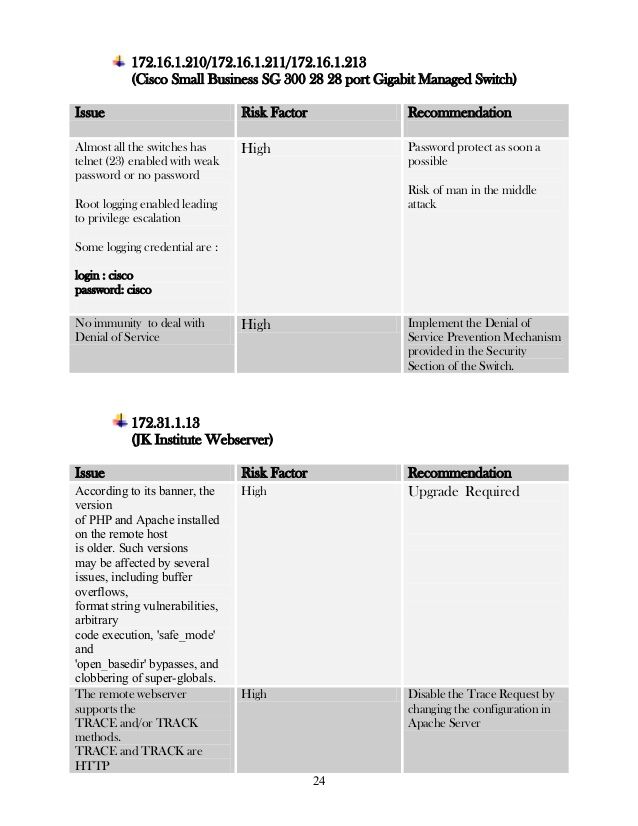
15 Jun The internal network consists of a combination firewall router and a hub. Both test machines are on the hub so that performing penetration tests is Nessus will report on vulnerabilities present on each host. Nessus Remote OS guesses: Cisco running IOS (6c), Cisco router running IOS
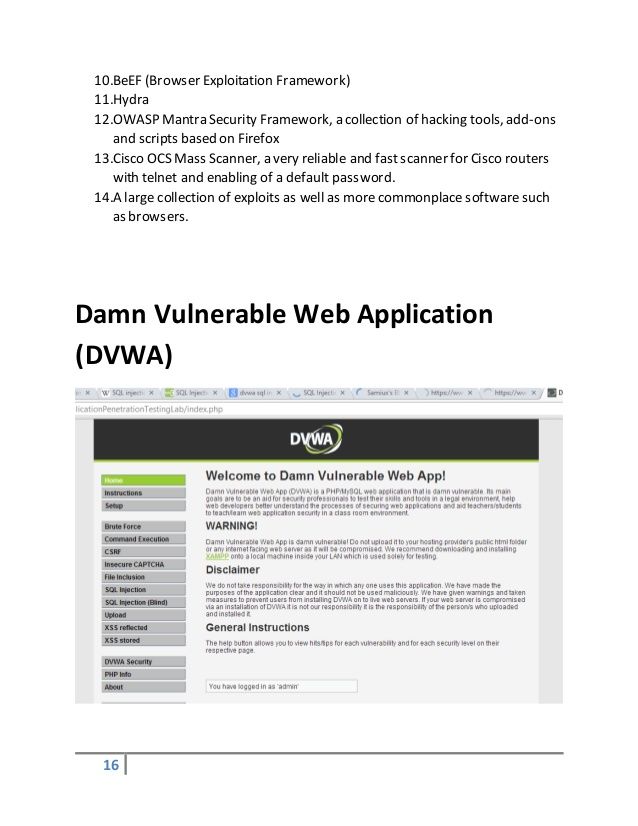
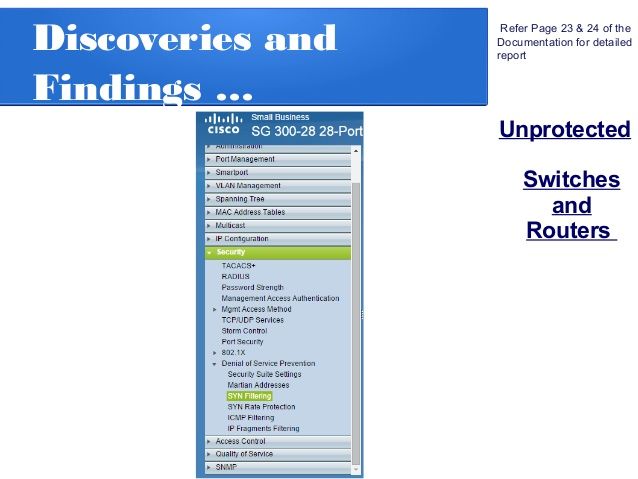
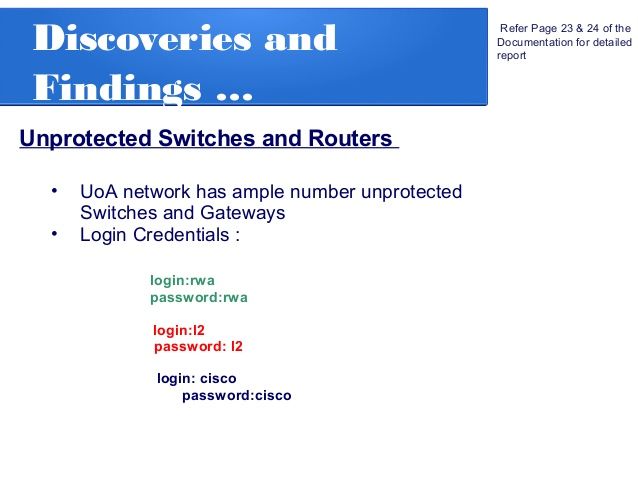
Description:With the latest release, we took this a step further and focused on accelerating the penetration testing process for Cisco IOS devices. While the individual modules and supporting libraries were added to the open source framework, the commercial products can now chain these modules together to quickly compromise all vulnerable devices on the network. The screen shot below gives you an idea of what a successful penetration test can look like: To begin with, I should state that a properly configured Cisco device is a tough target to crack. Vulnerabilities exist in IOS, just like any other piece of software, but only a few folks have managed to leverage memory corruption flaws into code execution. For this reason, the majority of real-world attacks against IOS devices tend to focus on two areas:
























User Comments 5
Post a comment
Comment: